Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
A user named User1 has a computer named Computer1 that runs Windows 10. Computer1 is joined to an Azure Active Directory (Azure AD) tenant named contoso.com. User1 joins Computer1 to contoso.com by using [email protected]
Computer1 contains a folder named Folder1. Folder1 is in drive C and is shared as Share1. Share1 has the permission shown in the following table.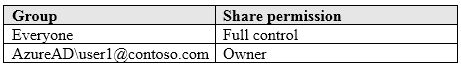
A user named User2 has a computer named Computer2 that runs Windows 10. User2 joins Computer2 to contoso.com by using [email protected]
User2 attempts to access Share1 and receives the following error message: `The username or password is incorrect.`
You need to ensure that User2 can connect to Share1.
Solution: You create a local group on Computer1 and add the Guest account to the group. You grant the group Modify access to Share1.
Does this meet the goal?
Answer:
B
Your network contains an Active Directory domain. The domain contains 1,000 computers that run Windows 10.
You need to prevent the computers of the research department from appearing in Network in File Explorer.
What should you do?
Answer:
C
HOTSPOT -
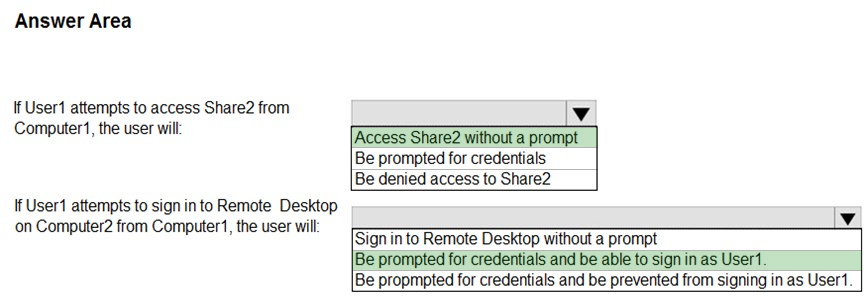
You have two computers named Computer1 and Computer2 that run Windows 10. The computers are in a workgroup.
You perform the following configurations on Computer1:
✑ Create a user named User1.
✑ Add User1 to the Remote Desktop Users group.
You perform the following configurations on Computer2:
✑ Create a user named User1 and specify the same user password as the one set on Computer1.
✑ Create a share named Share2 and grant User1 Full control access to Share2.
✑ Enable Remote Desktop.
What are the effects of the configurations? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area: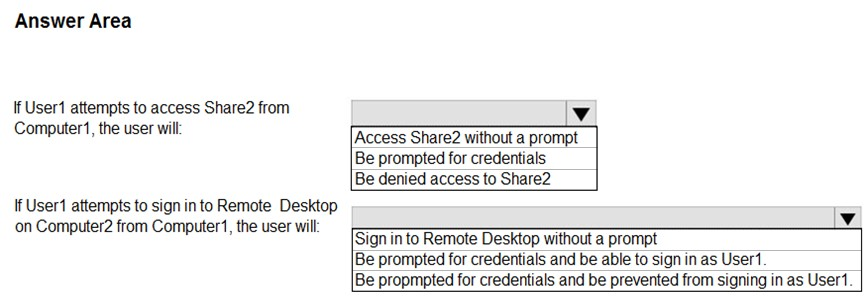
Answer:
HOTSPOT -
Your network contains an Active Directory domain. The domain contains a group named Group1.
All the computers in the domain run Windows 10. Each computer contains a folder named C:\Documents that has the default NTFS permissions set.
You add a folder named C:\Documents\Templates to each computer.
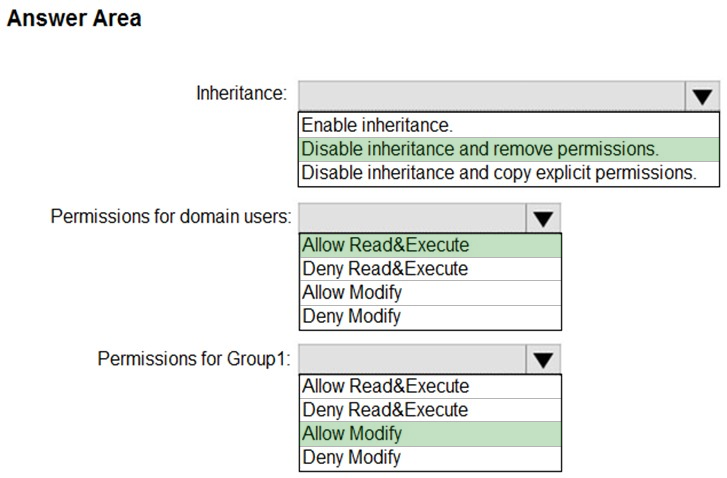
You need to configure the NTFS permissions to meet the following requirements:
✑ All domain users must be able to open the files in the Templates folder.
✑ Only the members of Group1 must be allowed to edit the files in the Templates folder.
How should you configure the NTFS settings on the Templates folder? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area: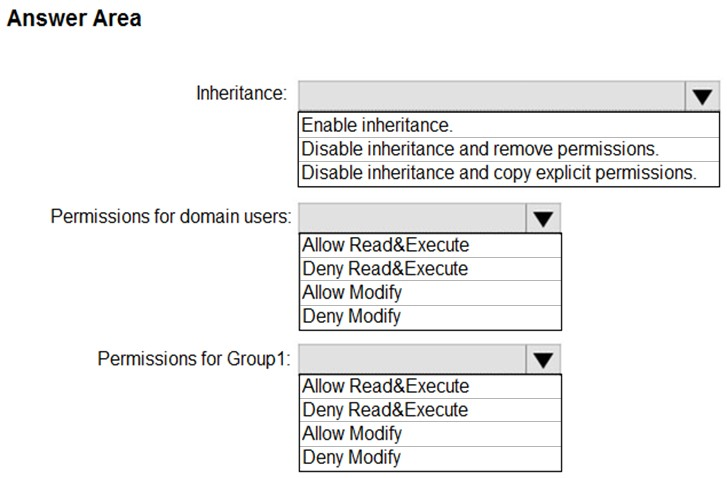
Answer:
You deploy Windows 10 to 20 new laptops.
The laptops will be used by users who work at customer sites. Each user will be assigned one laptop and one Android device.
You need to recommend a solution to lock the laptop when the users leave their laptop for an extended period.
Which two actions should you include in the recommendation? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
Answer:
DF
You have a workgroup computer named Computer1 that runs Windows 10. Computer1 has the user accounts shown in the following table.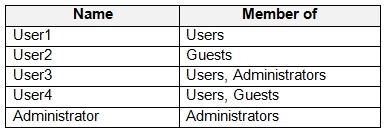
User3, User4, and Administrator sign in and sign out on Computer1. User1 and User2 have never signed in to Computer1.
You are troubleshooting policy issues on Computer1. You sign in to Computer1 as Administrator.
You add the Resultant Set of Policy (RSoP) snap-in to an MMC console.
Which users can you select in the RSoP wizard?
Answer:
D
When selecting users in RSoP, you can only select users who have previously logged on to the system.
HOTSPOT -
You have a computer named Computer1 that runs Windows 10. Computer1 is in a workgroup.
Computer1 contains the local users shown in the following table.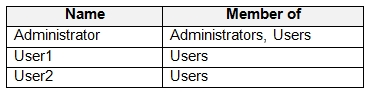
Computer1 contains the folders shown in the following table.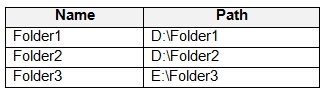
The Users group has Full control permissions to Folder1, Folder2, and Folder3.
User1 encrypts two files named File1.docx and File2.docx in Folder1 by using EFS.
Which users can move each file? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area: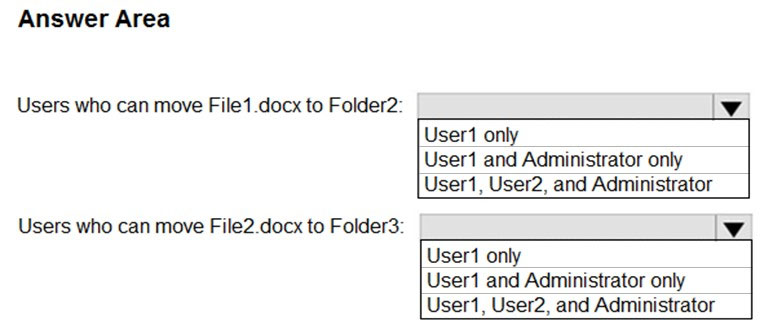
Answer:
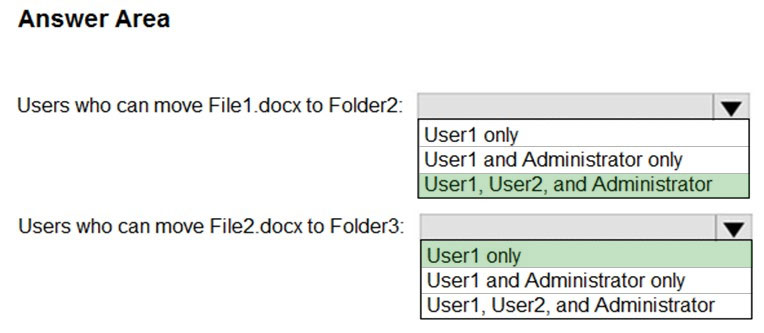
EFS works by encrypting a file with a bulk symmetric key. The symmetric key that is used to encrypt the file is then encrypted with a public key that is associated with the user who encrypted the file. Because the encryption & decryption operations are performed at a layer below NTFS, it is transparent to the user and all their applications.
Box 1: User1, User2, and Administrator
Box 2: User1 only
Your network contains an Active Directory domain. The domain contains a computer named Computer1 that runs Windows 10. Computer1 contains a folder named Folder1.
You plan to share Folder1. Everyone will have Read share permissions, and administrators will have Full control share permission.
You need to prevent the share from appearing when users browse the network.
What should you do?
Answer:
D
Appending a dollar sign to share name prevents a share from appearing when users browse the network.
Incorrect Answers:
Access-based enumeration will hide the share from anyone who doesn't have permission to access the share. However, as 'Everyone' has Read access to the share, the share would appear for everyone when they browse the network.
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a computer that runs Windows 10. The computer contains a folder. The folder contains sensitive data.
You need to log which user reads the contents of the folder and modifies and deletes files in the folder.
Solution: From the properties of the folder, you configure the Auditing settings and from Audit Policy in the local Group Policy, you configure Audit object access.
Does this meet the goal?
Answer:
A
Files and folders are objects and are audited through object access.
Reference:
https://www.netwrix.com/how_to_detect_who_changed_file_or_folder_owner.html
You have a computer named Computer1 that runs Windows 10.
On Computer1, you turn on File History.
You need to protect a folder named D:\Folder1 by using File History.
What should you do?
Answer:
C
To configure File History, click More options on the Backup screen. The Backup options screen allows you to set how often File History backs up your files and how long versions are saved.
Reference:
https://www.groovypost.com/howto/configure-windows-10-file-history/