You are building a Microsoft ASP.NET application that requires authentication.
You need to authenticate users by using Azure Active Directory (Azure AD).
What should you do first?
Answer:
B
Register your application to use Azure Active Directory. Registering the application means that your developers can use Azure AD to authenticate users and request access to user resources such as email, calendar, and documents.
Reference:
https://docs.microsoft.com/en-us/azure/active-directory/manage-apps/developer-guidance-for-integrating-applications
You have an Azure DevOps organization named Contoso.
You need to recommend an authentication mechanism that meets the following requirements:
✑ Supports authentication from Git
✑ Minimizes the need to provide credentials during authentication
What should you recommend?
Answer:
A
Personal access tokens (PATs) give you access to Azure DevOps and Team Foundation Server (TFS), without using your username and password directly.
These tokens have an expiration date from when they're created. You can restrict the scope of the data they can access. Use PATs to authenticate if you don't already have SSH keys set up on your system or if you need to restrict the permissions that are granted by the credential.
Incorrect Answers:
B: Azure DevOps no longer supports Alternate Credentials authentication since the beginning of March 2, 2020. If you're still using Alternate Credentials, we
[Microsoft] strongly encourage you to switch to a more secure authentication method (for example, personal access tokens).
Reference:
https://docs.microsoft.com/en-us/azure/devops/repos/git/auth-overview
You have an application that consists of several Azure App Service web apps and Azure functions.
You need to assess the security of the web apps and the functions.
Which Azure feature can you use to provide a recommendation for the security of the application?
Answer:
D
Monitor compute and app services: Compute & apps include the App Services tab, which App services: list of your App service environments and current security state of each.
Recommendations -
This section has a set of recommendations for each VM and computer, web and worker roles, Azure App Service Web Apps, and Azure App Service Environment that Security Center monitors. The first column lists the recommendation. The second column shows the total number of resources that are affected by that recommendation. The third column shows the severity of the issue.
Incorrect Answers:
C: Smart Detection automatically warns you of potential performance problems, not security problems in your web application.
Reference:
https://docs.microsoft.com/en-us/azure/azure-monitor/app/proactive-diagnostics
Your company has a project in Azure DevOps for a new web application.
The company identifies security as one of the highest priorities.
You need to recommend a solution to minimize the likelihood that infrastructure credentials will be leaked.
What should you recommend?
Answer:
B
Azure Key Vault provides a way to securely store credentials and other keys and secrets.
The Set-AzureKeyVaultSecret cmdlet creates or updates a secret in a key vault in Azure Key Vault.
Reference:
https://docs.microsoft.com/en-us/powershell/module/azurerm.keyvault/set-azurekeyvaultsecret
SIMULATION -
You need to ensure that an Azure web app named az400-123456789-main can retrieve secrets from an Azure key vault named az400-123456789-kv1 by using a system managed identity.
The solution must use the principle of least privilege.
To complete this task, sign in to the Microsoft Azure portal.
Answer:
See explanation below.
1. In Azure portal navigate to the az400-123456789-main app.
2. Scroll down to the Settings group in the left navigation.
3. Select Managed identity.
4. Within the System assigned tab, switch Status to On. Click Save.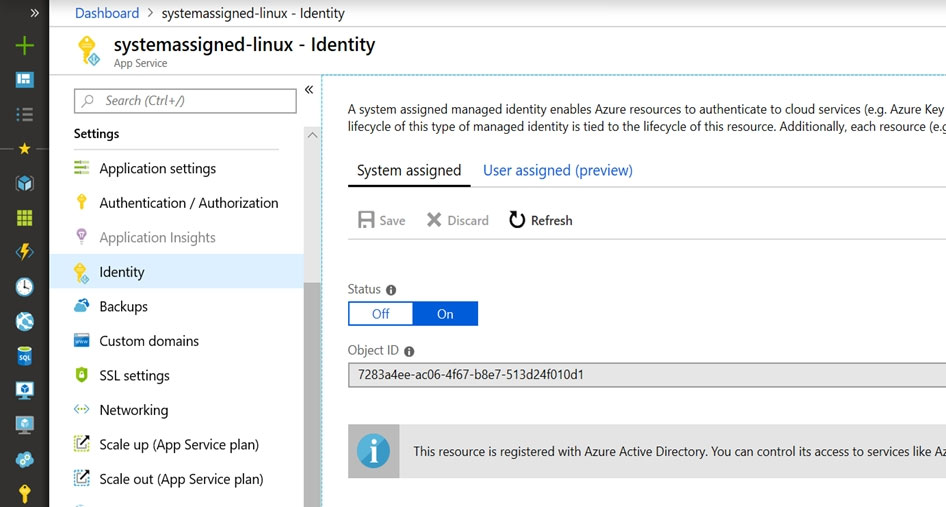
Reference:
https://docs.microsoft.com/en-us/azure/app-service/overview-managed-identity
You create a Microsoft ASP.NET Core application.
You plan to use Azure Key Vault to provide secrets to the application as configuration data.
You need to create a Key Vault access policy to assign secret permissions to the application. The solution must use the principle of least privilege.
Which secret permissions should you use?
Answer:
B
Application data plane permissions:
✑ Keys: sign
✑ Secrets: get
Reference:
https://docs.microsoft.com/en-us/azure/key-vault/key-vault-secure-your-key-vault
DRAG DROP -
Your company has a project in Azure DevOps.
You plan to create a release pipeline that will deploy resources by using Azure Resource Manager templates. The templates will reference secrets stored in Azure
Key Vault.
You need to recommend a solution for accessing the secrets stored in the key vault during deployments. The solution must use the principle of least privilege.
What should you include in the recommendation? To answer, drag the appropriate configurations to the correct targets. Each configuration may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.
Select and Place: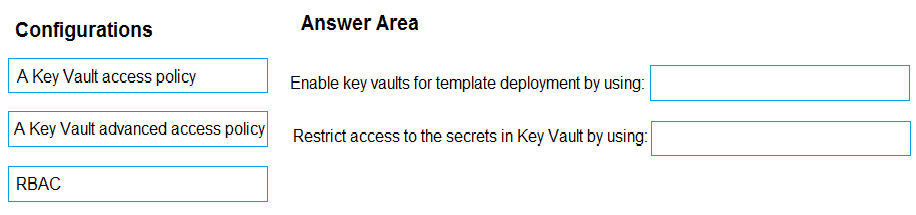
Answer:
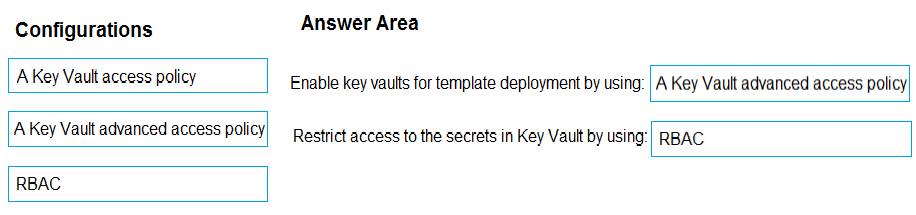
Box 1: A key Vault advanced access policy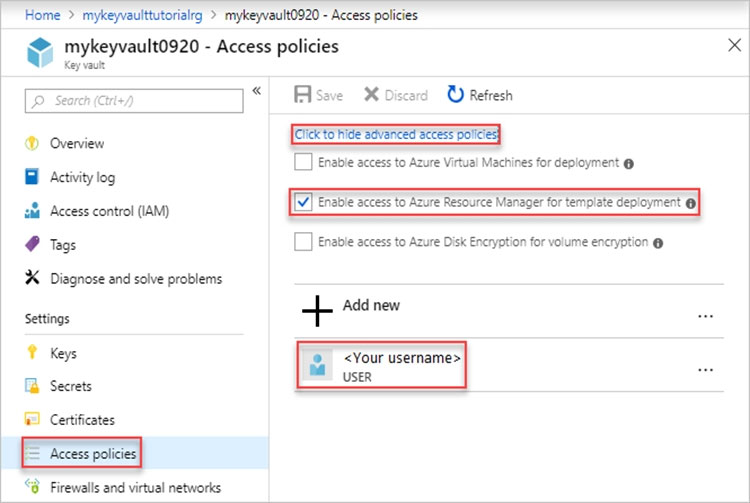
Box 2: RBAC -
Management plane access control uses RBAC.
The management plane consists of operations that affect the key vault itself, such as:
✑ Creating or deleting a key vault.
✑ Getting a list of vaults in a subscription.
✑ Retrieving Key Vault properties (such as SKU and tags).
✑ Setting Key Vault access policies that control user and application access to keys and secrets.
Reference:
https://docs.microsoft.com/en-us/azure/azure-resource-manager/resource-manager-tutorial-use-key-vault
DRAG DROP -
You need to configure access to Azure DevOps agent pools to meet the following requirements:
✑ Use a project agent pool when authoring build or release pipelines.
✑ View the agent pool and agents of the organization.
✑ Use the principle of least privilege.
Which role memberships are required for the Azure DevOps organization and the project? To answer, drag the appropriate role memberships to the correct targets. Each role membership may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.
Select and Place:
Answer:
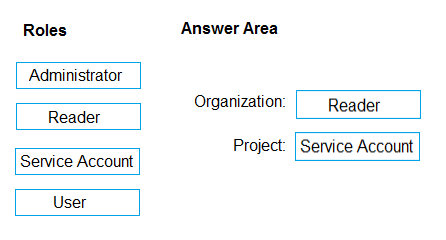
Box 1: Reader -
Members of the Reader role can view the organization agent pool as well as agents. You typically use this to add operators that are responsible for monitoring the agents and their health.
Box 2: Service account -
Members of the Service account role can use the organization agent pool to create a project agent pool in a project. If you follow the guidelines above for creating new project agent pools, you typically do not have to add any members here.
Incorrect Answers:
In addition to all the permissions given the Reader and the Service Account role, members of the administrator role can register or unregister agents from the organization agent pool. They can also refer to the organization agent pool when creating a project agent pool in a project. Finally, they can also manage membership for all roles of the organization agent pool. The user that created the organization agent pool is automatically added to the Administrator role for that pool.
Reference:
https://docs.microsoft.com/en-us/azure/devops/pipelines/agents/pools-queues
You have a branch policy in a project in Azure DevOps. The policy requires that code always builds successfully.
You need to ensure that a specific user can always merge changes to the master branch, even if the code fails to compile. The solution must use the principle of least privilege.
What should you do?
Answer:
D
In some cases, you need to bypass policy requirements so you can push changes to the branch directly or complete a pull request even if branch policies are not satisfied. For these situations, grant the desired permission from the previous list to a user or group. You can scope this permission to an entire project, a repo, or a single branch. Manage this permission along the with other Git permissions.
Reference:
https://docs.microsoft.com/en-us/azure/devops/repos/git/branch-policies
You have an Azure Resource Manager template that deploys a multi-tier application.
You need to prevent the user who performs the deployment from viewing the account credentials and connection strings used by the application.
What should you use?
Answer:
A
When you need to pass a secure value (like a password) as a parameter during deployment, you can retrieve the value from an Azure Key Vault. You retrieve the value by referencing the key vault and secret in your parameter file. The value is never exposed because you only reference its key vault ID. The key vault can exist in a different subscription than the resource group you are deploying to.
Reference:
https://docs.microsoft.com/en-us/azure/azure-resource-manager/resource-manager-keyvault-parameter