A company is building a data lake on Amazon S3. The data consists of millions of small files containing sensitive information. The Security team has the following requirements for the architecture:
* Data must be encrypted in transit.
* Data must be encrypted at rest.
* The bucket must be private, but if the bucket is accidentally made public, the data must remain confidential.
Which combination of steps would meet the requirements? (Choose two.)
BC
Bucket encryption using KMS will protect both in case disks are stolen as well as if the bucket is public.
This is because the KMS key would need to have privileges granted to it for users outside of AWS.
A Security Engineer discovered a vulnerability in an application running on Amazon ECS. The vulnerability allowed attackers to install malicious code. Analysis of the code shows it exfiltrates data on port 5353 in batches at random time intervals.
While the code of the containers is being patched, how can Engineers quickly identify all compromised hosts and stop the egress of data on port 5353?
C
An Amazon EC2 instance is denied access to a newly created AWS KMS CMK used for decrypt actions. The environment has the following configuration:
✑ The instance is allowed the kms:Decrypt action in its IAM role for all resources
✑ The AWS KMS CMK status is set to enabled
✑ The instance can communicate with the KMS API using a configured VPC endpoint
What is causing the issue?
D
In a key policy, you use "*" for the resource, which means "this CMK." A key policy applies only to the CMK it is attached to
Reference:
https://docs.aws.amazon.com/kms/latest/developerguide/key-policies.html
A company has enabled Amazon GuardDuty in all Regions as part of its security monitoring strategy. In one of the VPCs, the company hosts an Amazon EC2 instance working as an FTP server that is contacted by a high number of clients from multiple locations. This is identified by GuardDuty as a brute force attack due to the high number of connections that happen every hour.
The finding has been flagged as a false positive. However, GuardDuty keeps raising the issue. A Security Engineer has been asked to improve the signal-to-noise ratio. The Engineer needs to ensure that changes do not compromise the visibility of potential anomalous behavior.
How can the Security Engineer address the issue?
B
Trusted IP lists consist of IP addresses that you have whitelisted for secure communication with your AWS infrastructure and applications. GuardDuty does not generate findings for IP addresses on trusted IP lists. At any given time, you can have only one uploaded trusted IP list per AWS account per region.
Reference:
https://docs.aws.amazon.com/guardduty/latest/ug/guardduty_upload_lists.html
What are the MOST secure ways to protect the AWS account root user of a recently opened AWS account? (Choose two.)
BD
A company has decided to migrate sensitive documents from on-premises data centers to Amazon S3. Currently, the hard drives are encrypted to meet a compliance requirement regarding data encryption. The CISO wants to improve security by encrypting each file using a different key instead of a single key. Using a different key would limit the security impact of a single exposed key.
Which of the following requires the LEAST amount of configuration when implementing this approach?
D
Reference:
https://docs.aws.amazon.com/kms/latest/developerguide/services-s3.html
A company has an encrypted Amazon S3 bucket. An Application Developer has an IAM policy that allows access to the S3 bucket, but the Application Developer is unable to access objects within the bucket.
What is a possible cause of the issue?
C
Reference:
https://docs.aws.amazon.com/AmazonS3/latest/dev/example-bucket-policies.html
A Web Administrator for the website example.com has created an Amazon CloudFront distribution for dev.example.com, with a requirement to configure HTTPS using a custom TLS certificate imported to AWS Certificate Manager.
Which combination of steps is required to ensure availability of the certificate in the CloudFront console? (Choose two.)
BD
A Security Engineer has discovered that, although encryption was enabled on the Amazon S3 bucket examplebucket, anyone who has access to the bucket has the ability to retrieve the files. The Engineer wants to limit access to each IAM user can access an assigned folder only.
What should the Security Engineer do to achieve this?
D
Reference:
https://aws.amazon.com/premiumsupport/knowledge-center/iam-s3-user-specific-folder/
A Security Engineer manages AWS Organizations for a company. The Engineer would like to restrict AWS usage to allow Amazon S3 only in one of the organizational units (OUs). The Engineer adds the following SCP to the OU: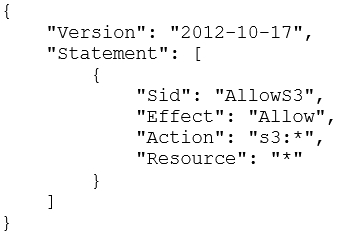
The next day, API calls to AWS IAM appear in AWS CloudTrail logs in an account under that OU.
How should the Security Engineer resolve this issue?
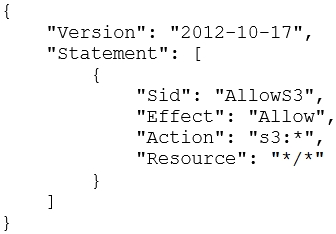
B
Reference:
https://docs.aws.amazon.com/organizations/latest/userguide/organizations-userguide.pdf
(22)